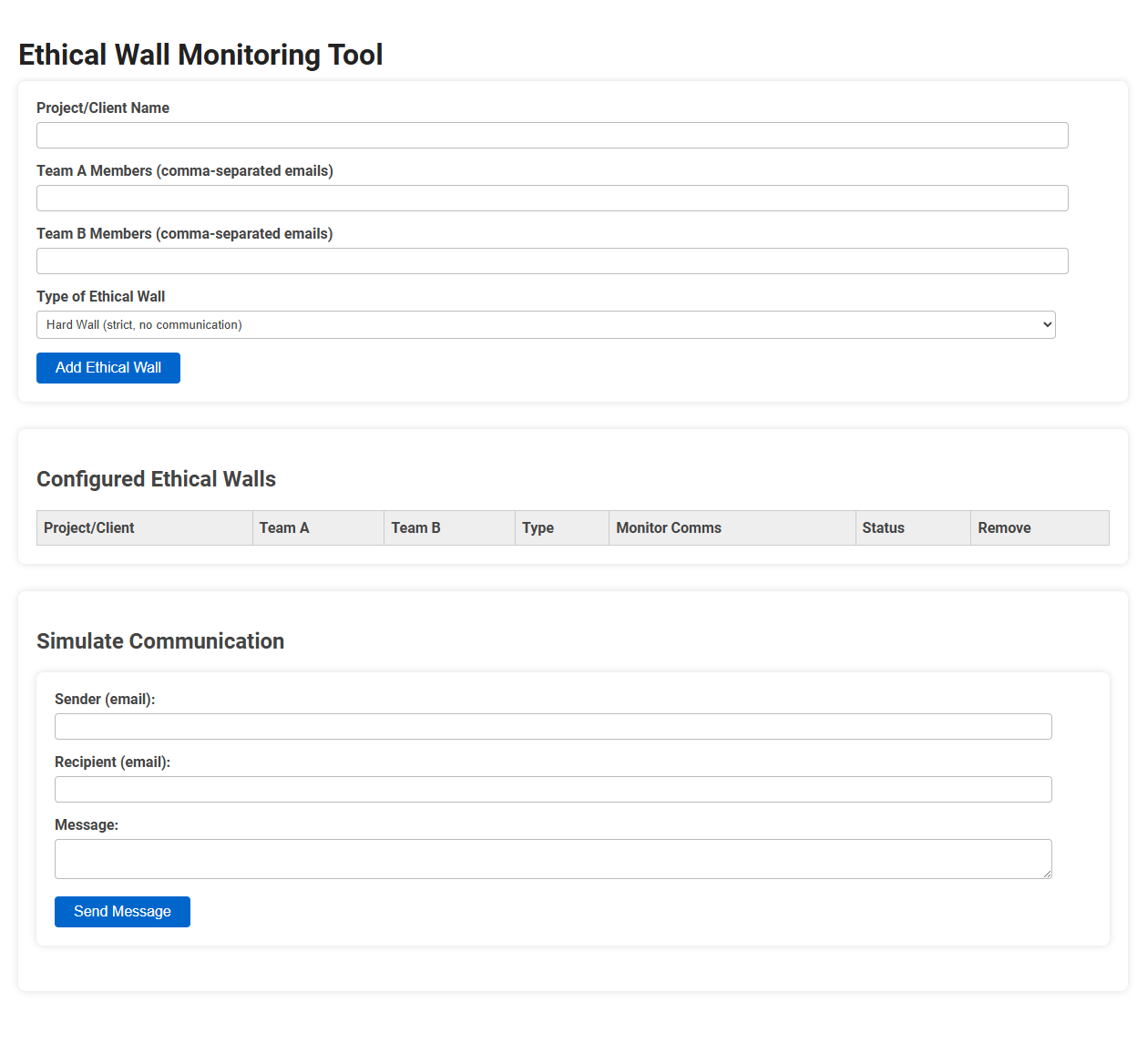
The Ethical Wall Monitoring Tool is a compliance solution designed to prevent unauthorized communication between designated teams or individuals within an organization by configuring and monitoring ethical walls. It is essential for industries where data protection, confidentiality, and conflict of interest controls are required, such as legal, finance, and consulting sectors. Its usage involves setting up strict or monitored communication barriers for projects or clients by specifying team members and wall types, and it allows administrators to simulate and monitor communications to ensure policy adherence.
How to use this tool?
Complete Guide to Using the Ethical Wall Monitoring Tool
-
Configure an Ethical Wall
-
Enter Project/Client Name:
Enter the name of the relevant project or client in the provided text field. -
Specify Team Members:
- In "Team A Members," enter the email addresses of all Team A members, separated by commas.
- In "Team B Members," enter the email addresses of all Team B members, separated by commas. -
Select Type of Ethical Wall:
Choose the type of wall (e.g., "Hard Wall") from the dropdown list. "Hard Wall" typically means no communication allowed between the specified teams. -
Add Ethical Wall:
Click the "Add Ethical Wall" button to save the configuration. The wall will appear in the "Configured Ethical Walls" table.
-
Enter Project/Client Name:
-
Review Configured Ethical Walls
- All configured walls are listed under the "Configured Ethical Walls" section.
- Details shown include Project/Client, Team A & B, Type, Monitoring settings, Status, and a Remove option for deleting a wall. -
Simulate Communication
-
Fill Communication Details:
- Enter the sender's email in the "Sender" field.
- Enter the recipient's email in the "Recipient" field.
- Write your message in the "Message" box. -
Send Message:
Click "Send Message" to simulate a communication. The system will check the configured ethical walls and display whether the message is allowed or blocked based on the wall rules.
-
Fill Communication Details:
-
Managing Ethical Walls
- To remove a configured wall, click the "Remove" option in the corresponding row.
- Status and monitoring options let you track which walls are active and communication monitoring status.
Tips
- Always ensure emails are correctly entered and separated by commas.
- Use the simulation feature to test your configuration before deploying to real-world scenarios.
- Regularly review ethical wall status to ensure compliance and update as teams or projects change.
Introduction to Ethical Wall Compliance
An Ethical Wall Monitoring Tool ensures compliance by preventing unauthorized information flow within your organization, safeguarding sensitive data and maintaining regulatory standards. Implementing such a system aligns with industry regulations like GDPR and HIPAA, minimizing the risk of data breaches and insider threats. You can enhance trust and transparency by systematically enforcing information barriers across departments.
Importance of Automated Ethical Wall Monitoring
Automated Ethical Wall Monitoring tools play a crucial role in maintaining compliance by preventing unauthorized information flow between restricted groups within an organization. These tools use advanced algorithms to detect and isolate conflicts of interest, ensuring data integrity and reducing legal risks. Implementing automated monitoring enhances operational efficiency while safeguarding sensitive communications against potential breaches.
Getting Started with the Free Online Tool
Ethical wall monitoring tools help organizations prevent unauthorized information flow by enforcing communication barriers within teams. Getting started with the free online tool requires setting up user roles and defining policy rules to ensure compliant data segregation. This streamlined setup enables quick deployment and effective monitoring without extensive technical knowledge.
Configuring Your First Ethical Wall
Configuring your first ethical wall involves setting clear parameters to prevent unauthorized information sharing between departments or teams. Ethical wall monitoring tools use predefined rules and access controls to enforce these barriers, ensuring compliance with regulatory standards and protecting sensitive data. Proper setup includes defining user roles, communication channels, and exception handling to maintain organizational integrity and mitigate conflict of interest risks.
Assigning Teams and Managing Member Access
Assigning teams in an ethical wall monitoring tool ensures sensitive information is compartmentalized based on your organizational structure. Managing member access controls who views or interacts with restricted data, maintaining compliance and preventing conflicts of interest. This streamlined approach strengthens your data security and regulatory adherence.
Selecting the Appropriate Ethical Wall Type
Selecting the appropriate ethical wall type depends on the organization's specific compliance requirements and data sensitivity levels. Common types include physical barriers, digital access controls, and policy-driven workflows designed to prevent conflicts of interest and unauthorized information sharing. An effective ethical wall monitoring tool integrates these methods to ensure robust segregation and real-time oversight.
Real-Time Simulation for Compliance Testing
Ethical wall monitoring tools employ real-time simulation to enhance compliance testing by replicating sensitive information barriers within organizations. This technology enables proactive detection of potential data breaches and ensures adherence to regulatory standards such as GDPR and SEC rules. Real-time simulation facilitates dynamic testing environments that improve the accuracy and effectiveness of compliance risk assessments.
Monitoring and Reviewing Active Walls
An ethical wall monitoring tool enables continuous oversight of active walls, ensuring sensitive information remains compartmentalized within your organization. By systematically reviewing communication patterns and access logs, you can quickly detect and address potential breaches or conflicts of interest. This proactive monitoring safeguards compliance with legal and regulatory standards, maintaining trust and integrity in your operations.
Best Practices for Maintaining Compliance
An ethical wall monitoring tool enforces communication barriers within organizations to prevent conflicts of interest and safeguard sensitive information. Best practices for maintaining compliance include regularly updating access controls based on role changes, conducting frequent audits to detect unauthorized information crossover, and implementing automated alerts for policy violations. Leveraging machine learning algorithms enhances anomaly detection and supports continuous improvement in compliance efforts.
Ethical wall monitoring tool Tool Preview