The SHA256 Hash Generator tool converts any input text into a secure, fixed-length SHA-256 hash value. This tool is widely used for password hashing, data integrity verification, and cryptographic security applications. Users simply enter their desired text and generate its hash instantly for secure processing or validation needs.
How to use this tool?
Complete Guide: How to Use the SHA256 Hash Generator Tool
-
Access the Tool:
Go to the web page where the SHA256 Hash Generator tool is hosted. -
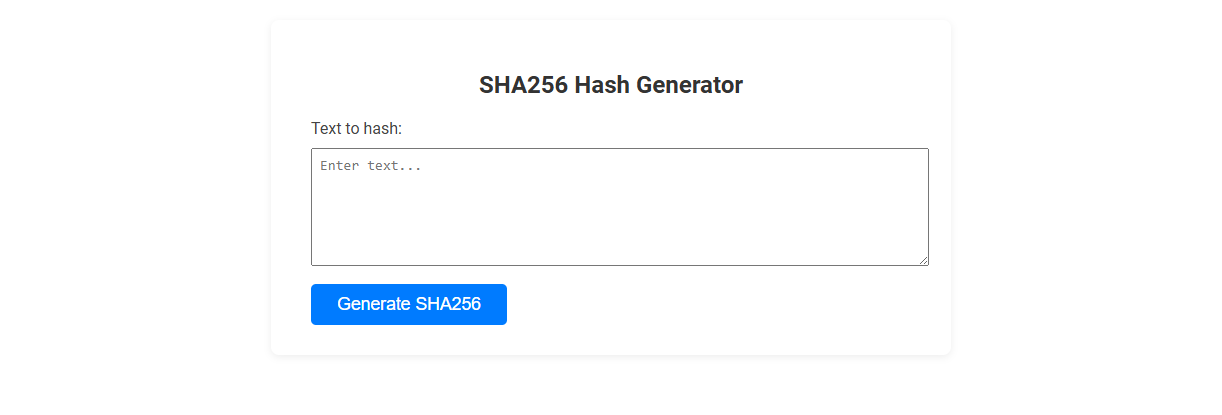
Locate the Input Box:
You will see a text area labeled "Text to hash:" with a placeholder saying Enter text.... -
Enter Your Text:
Click on the input area and type or paste the text you want to generate a SHA256 hash for. -
Generate the Hash:
Once your text is entered, click the "Generate SHA256" button below the input box. -
View the Output:
The generated SHA256 hash will be displayed on the page, usually below the button. -
Copy the Result (Optional):
Select and copy the hash string if you need to use it elsewhere.
Tips:
- SHA256 hashes are one-way functions; you cannot reverse them to get the original text.
- Make sure there are no unwanted spaces or extra characters in your input for accurate results.
- This tool is helpful for generating digital fingerprints of text, passwords, or files for security purposes.
Introduction to SHA256 Hash Generation Tools
SHA256 hash generators create fixed-length, 256-bit cryptographic hashes from input data, ensuring data integrity and security in digital communications. These tools are widely used in cybersecurity, blockchain, and software development for verifying file authenticity and password protection. Advanced SHA256 hash generators offer fast processing, compatibility with multiple file types, and real-time hash calculation.
Benefits of Free Online SHA256 Hash Generators for Developers
Free online SHA256 hash generators provide developers with quick and easy access to secure hashing without the need for software installation. These tools enhance your workflow by ensuring data integrity and verifying file authenticity instantly. Utilizing a free online SHA256 hash generator saves time and resources, allowing you to focus on development tasks efficiently.
How SHA256 Hashing Works in Application Security
SHA256 Hash Generator creates a fixed 256-bit hash value from input data, ensuring data integrity and authentication in application security. By transforming sensitive information into unique hashes, it prevents exposure of original data during storage or transmission. Developers use SHA256 hashing to verify data authenticity and protect against tampering and cyber attacks.
Step-by-Step Guide: Using the Online SHA256 Hash Generator
Step-by-Step Guide: Using the Online SHA256 Hash Generator Enter the text or file you want to hash into the input field of the SHA256 Hash Generator. Click the "Generate" button to process the data and produce a unique 256-bit hash value. Copy the resulting SHA256 hash for verification, security, or data integrity purposes.
Key Features of the SHA256 Hash Generator Tool
The SHA256 Hash Generator Tool produces fixed-length 256-bit hash values from any input data, ensuring data integrity and secure encryption. It supports high-speed processing with minimal collision probability, making it ideal for cryptographic applications and digital signatures. The tool offers easy integration through APIs and cross-platform compatibility for seamless use in various programming environments.
Best Practices for Secure Hash Generation
Secure hash generation with a SHA256 Hash Generator requires using a cryptographically secure random salt to prevent rainbow table attacks. You should implement key stretching techniques like PBKDF2 or bcrypt to enhance hash resilience against brute-force attempts. Regularly update your hashing algorithms to adhere to the latest security standards and protect sensitive data effectively.
Common Developer Use Cases for SHA256 Hashes
SHA256 hash generators are essential tools for developers to ensure data integrity, securely store passwords, and verify file authenticity. Common use cases include generating unique digital fingerprints for files to detect tampering, creating secure password hashes resistant to brute-force attacks, and enabling blockchain transaction verification. These applications leverage SHA256's cryptographic strength to enhance security and trust in software systems.
Comparing Online SHA256 Tools: What to Look For
Comparing online SHA256 hash generator tools requires evaluating processing speed, output accuracy, and user interface simplicity to ensure reliable and efficient hashing. Security features such as data privacy policies and encryption methods are critical for protecting sensitive input during hash computation. Choose platforms that support bulk hashing and provide clear, verifiable results to optimize workflow and maintain data integrity.
Integrating SHA256 Hash Generation into Developer Workflows
Integrating a SHA256 hash generator into developer workflows enhances data integrity verification by providing a secure, consistent method to create unique digital fingerprints. Developers can automate hash generation within CI/CD pipelines, ensuring code authenticity and simplifying change tracking. Utilizing SHA256 streamlines version control and data validation, crucial for robust software development practices.
SHA256 Hash Generator Tool Preview